Overview of the CompTIA CAS-004 Exam
The CompTIA Advanced Security Practitioner (CASP+) CAS-004 certification is designed for experienced security professionals looking to enhance their expertise in enterprise security, risk management, and incident response. As a performance-based exam, the CAS-004 tests candidates on their ability to apply advanced security solutions in real-world scenarios. This certification is particularly relevant for IT security practitioners, cybersecurity analysts, and penetration testers who work in the field of information security.
The CAS-004 exam covers various domains, including risk management, enterprise security operations, architecture, research, collaboration, and integration of advanced security solutions. One of the key areas examined is cyberwarfare—an essential component of modern cybersecurity strategies. Given the increasing sophistication of cyber threats, security professionals must be well-versed in cyberwarfare tactics and defensive measures to protect critical infrastructure and sensitive data.
Explanation of Cyberwarfare as a Modern Warfare Strategy
Cyberwarfare refers to the use of digital attacks by nations, organizations, or individuals to disrupt, sabotage, or manipulate an adversary's digital infrastructure. Unlike traditional warfare, which involves physical force, cyberwarfare operates in the digital domain and targets information systems, networks, and digital assets.
Governments and private organizations recognize cyberwarfare as a critical component of national security. It can be used to weaken an enemy’s economy, disrupt communication channels, and even influence political outcomes. Given its far-reaching implications, cybersecurity professionals must understand the various aspects of cyberwarfare to effectively mitigate risks and implement protective measures.
The Main Purpose of Cyberwarfare
Cyberwarfare serves multiple strategic purposes. Governments, criminal organizations, and hacktivists use it to achieve military, economic, and political objectives. Below are the key purposes of cyberwarfare:
1. Disruption of Critical Infrastructure
One of the primary goals of cyberwarfare is to disrupt essential services such as power grids, water supplies, healthcare systems, and transportation networks. A well-coordinated cyberattack on a nation's infrastructure can lead to significant economic losses, loss of life, and national security threats.
For example, the Stuxnet worm, a malicious computer worm discovered in 2010, was allegedly developed to target Iran's nuclear facilities. It disrupted industrial control systems and significantly set back Iran's nuclear program, demonstrating the potential power of cyberwarfare in targeting critical infrastructure.
2. Espionage and Intelligence Gathering
Cyberwarfare is often used to gather intelligence on foreign governments, military operations, corporations, and influential individuals. Cyber espionage involves the theft of sensitive data, trade secrets, military plans, and classified documents.
Nation-state actors frequently engage in cyber espionage to gain strategic advantages. Groups like APT29 (Cozy Bear) and APT28 (Fancy Bear) have been linked to cyber espionage campaigns targeting government institutions, media organizations, and private businesses. Such operations provide adversaries with valuable intelligence that can be leveraged for political or military purposes.
3. Sabotage and Destruction
Cyberwarfare can also be used to cause direct destruction of an adversary’s digital assets or disrupt operational capabilities. Malicious actors deploy ransomware, Distributed Denial-of-Service (DDoS) attacks, and destructive malware to sabotage organizations and governments.
For instance, the NotPetya malware attack in 2017, initially disguised as ransomware, was later found to be a state-sponsored attack designed to cause widespread disruption. It crippled businesses, including Maersk, FedEx, and Merck, resulting in billions of dollars in damages.
4. Psychological and Political Manipulation
Cyberwarfare is not limited to infrastructure attacks; it is also used as a tool for psychological and political manipulation. Cyber actors spread disinformation, propaganda, and fake news to influence public perception, manipulate elections, and create social unrest.
During the 2016 U.S. presidential election, various cyber operations were conducted to spread disinformation through social media platforms. These tactics aimed to sway public opinion and create divisions within society. Psychological warfare in cyberspace has become an effective means of influencing political outcomes without direct military engagement.
5. Economic Warfare
Cyberwarfare can be deployed to weaken a nation’s economy by targeting financial institutions, stock markets, and major corporations. Cyberattacks on banks, payment systems, and financial networks can cause market instability and economic disruptions.
For example, cybercriminals have launched attacks on SWIFT, the global banking messaging system, to steal millions of dollars from financial institutions. Economic cyberwarfare can also involve intellectual property theft, which costs businesses billions of dollars annually.
Cyberwarfare in the Context of the CompTIA CAS-004 Exam
Understanding cyberwarfare is essential for professionals preparing for the CAS-004 exam, as the certification covers advanced security concepts related to cyber threats and mitigation strategies. The exam tests candidates on their ability to analyze security incidents, respond to cyber threats, and implement risk management frameworks.
Security professionals must be familiar with the tactics, techniques, and procedures (TTPs) used in cyberwarfare. The CAS-004 exam evaluates candidates’ knowledge in the following areas:
-
Threat Intelligence and Cyberwarfare Tactics: Understanding how cyber adversaries operate and the methodologies they use in launching attacks.
-
Advanced Persistent Threats (APTs): Recognizing and mitigating threats from nation-state actors and sophisticated cybercriminal organizations.
-
Incident Response and Digital Forensics: Developing an incident response plan to detect, analyze, and respond to cyberattacks.
-
Security Operations and Risk Management: Implementing cybersecurity frameworks and best practices to safeguard critical infrastructure from cyberwarfare.
-
Enterprise Security Architecture: Designing resilient security architectures to protect against cyber threats and ensure business continuity.
By mastering these concepts, CAS-004 candidates can enhance their ability to defend against cyberwarfare threats and contribute to the cybersecurity resilience of organizations and governments.
Conclusion
Cyberwarfare has become an integral part of modern warfare, influencing geopolitical conflicts, economic stability, and national security. With increasing cyber threats from nation-state actors, criminal organizations, and hacktivists, security professionals must be well-equipped to handle cyberwarfare challenges.
The CompTIA CAS-004 certification provides IT security practitioners with the skills needed to analyze cyber threats, respond to security incidents, and implement robust security frameworks. By obtaining the CAS-004 certification, professionals can enhance their careers and play a crucial role in defending against cyberwarfare tactics.
For individuals preparing for the CAS-004 exam, DumpsBoss offers a comprehensive collection of exam resources, including practice questions, study guides, and expert-verified dumps. These resources can help candidates strengthen their knowledge and improve their chances of passing the exam successfully.
Investing in cybersecurity education and certifications like CAS-004 is essential for staying ahead in the rapidly evolving field of cybersecurity. With the right preparation, security professionals can effectively combat cyberwarfare threats and contribute to a safer digital landscape.
Special Discount: Offer Valid For Limited Time “CAS-004 Exam” Order Now!
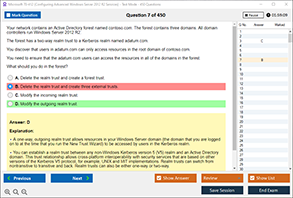
Sample Questions for CompTIA CAS-004 Dumps
Actual exam question from CompTIA CAS-004 Exam.
What is the main purpose of cyberwarfare?
A) To improve internet speed globally
B) To launch cyberattacks for espionage, disruption, or sabotage
C) To develop new cybersecurity software
D) To enhance online gaming performance