Introduction to the CompTIA SY0-701 Exam
The CompTIA SY0-701 exam is a cornerstone certification for cybersecurity professionals. It validates the skills and knowledge required to secure networks, manage risks, and respond to incidents effectively. The exam covers a wide range of topics, including threat management, cryptography, identity management, and, crucially, the handling of digital evidence.
One of the key areas tested in the SY0-701 exam is the concept of the chain of custody. This is a legal and procedural framework that ensures the integrity of evidence from the moment it is collected until it is presented in court. Understanding and implementing a robust chain of custody is essential for any cybersecurity professional, as it directly impacts the credibility and admissibility of evidence in legal proceedings.
Definition of CompTIA SY0-701 Exam
The CompTIA SY0-701 exam, also known as the CompTIA Security+ certification, is designed to validate the baseline skills necessary to perform core security functions and pursue an IT security career. The exam covers a broad spectrum of topics, including:
- Threats, Attacks, and Vulnerabilities: Understanding different types of malware, social engineering attacks, and vulnerabilities in systems.
- Technologies and Tools: Familiarity with various security technologies and tools used to protect networks and systems.
- Architecture and Design: Knowledge of secure network architecture, system design, and cloud security.
- Identity and Access Management: Implementing identity and access management controls to protect sensitive information.
- Risk Management: Assessing and mitigating risks to organizational security.
- Cryptography and PKI: Understanding cryptographic concepts and public key infrastructure (PKI).
Within these domains, the exam places significant emphasis on the proper handling of digital evidence, particularly the chain of custody. This is because the integrity of evidence is paramount in cybersecurity investigations, and any lapse in the chain of custody can render evidence inadmissible in court.
Key Elements Required to Prove Chain of Custody
The chain of custody is a chronological documentation that shows the seizure, control, transfer, analysis, and disposition of physical or electronic evidence. To prove a chain of custody, several key elements must be established:
- Documentation: Every step of the evidence handling process must be meticulously documented. This includes who collected the evidence, when and where it was collected, and how it was stored and transferred.
- Identification: Each piece of evidence must be uniquely identified. This can be done through tagging, labeling, or other means of identification that ensure the evidence can be easily tracked.
- Storage: Evidence must be stored in a secure manner to prevent tampering, loss, or degradation. This often involves using tamper-evident seals, secure storage facilities, and access controls.
- Transfer: When evidence is transferred from one person or location to another, the transfer must be documented. This includes the names of the individuals involved, the date and time of the transfer, and the method of transfer.
- Access Control: Only authorized personnel should have access to the evidence. Access logs should be maintained to track who has accessed the evidence and when.
- Integrity Checks: Regular integrity checks should be performed to ensure that the evidence has not been altered or tampered with. This can involve using cryptographic hashes or other methods to verify the integrity of the data.
By establishing these elements, cybersecurity professionals can ensure that the chain of custody is maintained, and the evidence remains admissible in court.
Consequences of Breaking the Chain of Custody
Breaking the chain of custody can have severe consequences, both legally and professionally. When the chain of custody is compromised, the integrity of the evidence is called into question, and it may be deemed inadmissible in court. This can result in the dismissal of charges, the acquittal of the accused, or the inability to prosecute a case.
In addition to legal consequences, breaking the chain of custody can damage the reputation of the cybersecurity professional and their organization. It can lead to a loss of trust from clients, partners, and stakeholders, and can have long-term implications for the professional's career.
Moreover, breaking the chain of custody can undermine the entire investigation. Without reliable evidence, it becomes difficult to identify the source of a security breach, assess the extent of the damage, or take appropriate remedial actions. This can leave the organization vulnerable to further attacks and increase the overall risk to its security.
Best Practices for Maintaining Chain of Custody
Given the critical importance of the chain of custody, it is essential to follow best practices to ensure its integrity. Here are some key best practices for maintaining the chain of custody:
- Develop a Standard Operating Procedure (SOP): Establish a clear and comprehensive SOP for handling digital evidence. This should outline the steps for collecting, documenting, storing, and transferring evidence, as well as the roles and responsibilities of the personnel involved.
- Train Personnel: Ensure that all personnel involved in handling evidence are properly trained on the SOP and understand the importance of maintaining the chain of custody. Regular training sessions and refresher courses can help reinforce these practices.
- Use Tamper-Evident Seals: When collecting and storing evidence, use tamper-evident seals to prevent unauthorized access or tampering. These seals provide a visual indication if the evidence has been compromised.
- Maintain Detailed Documentation: Keep detailed records of every step in the evidence handling process. This includes who collected the evidence, when and where it was collected, how it was stored, and who had access to it. Documentation should be clear, concise, and accurate.
- Implement Access Controls: Restrict access to evidence to authorized personnel only. Use access logs to track who has accessed the evidence and when. This helps ensure accountability and prevents unauthorized tampering.
- Conduct Regular Audits: Perform regular audits of the evidence handling process to identify any potential weaknesses or areas for improvement. Audits can help ensure that the SOP is being followed and that the chain of custody is being maintained.
- Use Cryptographic Hashes: When dealing with digital evidence, use cryptographic hashes to verify the integrity of the data. A cryptographic hash is a unique string of characters that is generated based on the contents of a file. By comparing the hash of the original file with the hash of the file after it has been transferred or stored, you can verify that the file has not been altered.
- Secure Storage Facilities: Store evidence in secure facilities that are protected against unauthorized access, environmental hazards, and other risks. This may include using locked cabinets, secure rooms, or off-site storage facilities.
- Limit the Number of Handlers: Minimize the number of people who handle the evidence. Each time evidence is transferred, there is a risk of contamination or tampering. By limiting the number of handlers, you can reduce this risk.
- Use Digital Evidence Management Systems: Consider using digital evidence management systems (DEMS) to automate and streamline the evidence handling process. DEMS can help ensure that all steps are documented, access is controlled, and integrity checks are performed.
By following these best practices, cybersecurity professionals can ensure that the chain of custody is maintained, and the integrity of the evidence is preserved.
Conclusion
The CompTIA SY0-701 exam is a critical certification for cybersecurity professionals, and mastering the concept of the chain of custody is essential for success. The chain of custody ensures the integrity and admissibility of evidence, and any lapse in this process can have severe consequences.
By understanding the key elements required to prove the chain of custody, recognizing the consequences of breaking it, and following best practices for maintaining it, cybersecurity professionals can enhance their skills and improve their ability to handle digital evidence effectively.
Whether you're preparing for the SY0-701 exam or looking to strengthen your cybersecurity expertise, a solid understanding of the chain of custody is indispensable. By adhering to the principles outlined in this guide, you can ensure that your evidence handling processes are robust, reliable, and legally sound.
In the fast-paced world of cybersecurity, staying ahead of threats requires not only technical expertise but also a commitment to best practices and ethical standards. By mastering the chain of custody, you can contribute to the integrity of cybersecurity investigations and help protect organizations from the ever-present threat of cyberattacks.
Special Discount: Offer Valid For Limited Time “SY0-701 Exam” Order Now!
Sample Questions for CompTIA SY0-701 Dumps
Actual exam question from CompTIA SY0-701 Exam.
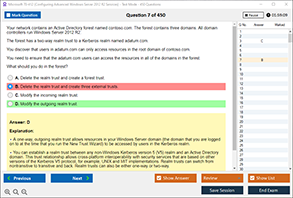
When performing computer forensics, what is required to prove a chain of custody?
A) A detailed log of all interactions with the evidence
B) A photograph of the suspect's computer
C) A witness testimony from the suspect
D) A copy of the suspect's browsing history